I have been writing about automated law--data driven governance the object of which is to automate the system for managing the behaviors of individuals and institutions through the imposition of systems of punishments and rewards that are tied to lists onto which people (and entities) are placed as a result of the application of objectives based analytics to analytics-relevant data (e.g., here, here, and here). That is a mouthful--to be sure. Yet a careful parsing suggests the transformative elements of automated law--though the object remains unchanged (to get people to obey a rule or conform to a norm articulated through law or directive (itself derived from some lawful source created in some lawful manner) but automated in the sense that enforcement does not require the exercise of administrative or judicial power.
The basis for this enterprise is data. The importance of this element of automated law is inversely related the attention paid to data by those who worry (from liberal democratic and Marxist-Leninist perspectives) about the integrity of data driven governance and it collateral effects (especially its effects on the integrity of conventional law systems). That is a pity. The issue of integrity is quite distinct from but no less important that the grounding premises from which analysts and coders translate the language of objectives into language that makes it measurable and then on that basis select those its of "facts" (information that becomes "facts" in the context of the analytics even if in other context it might be opinion, for example). While data choice goes to the construction of building blocks for analytics, data integrity goes to the issue of the reliability of the data (the information treated as "fact" for purposes of coding) is actually what it stands for, and that it can be protected from interference by others.
| Source Verve |
The first constitutes self-reflexive corruption. It is the sort of resistance by the objects of data harvesting that itself might become the object of data driven governance; but it also suggests that the objects of data harvesting are not to be assumed to be a constantly reliable source of information (other than information about their willingness NOT to provide truthful information). Robust data harvesting must include back-up or conforming sources. Here we have system failure.
The second constitutes internal corruption. It marks the fundamental illegitimacy of the system of data driven governance where it serves as a cover for arbitrary decision making. It is usually evidenced by the insertion of false information by state agents, or by the agents of the operators of the data governance (usually private) system, to further the personal or local institutional aims of the officials engaging in the practice. Here we have system legitimacy.
 The third constitutes external corruption. It is the sort of action that represents the failure to protect the integrity of the system (and its data) from outsiders. It calls into question the integrity of the system (e.g., it becomes unclear who inserted data into the data warehouse, or to what ends; or why data was extracted from the warehouse). It serves to expose the lack of systemic robustness. Here one encountered the possibility of systemic manipulation--sometimes observable and sometimes not.
The third constitutes external corruption. It is the sort of action that represents the failure to protect the integrity of the system (and its data) from outsiders. It calls into question the integrity of the system (e.g., it becomes unclear who inserted data into the data warehouse, or to what ends; or why data was extracted from the warehouse). It serves to expose the lack of systemic robustness. Here one encountered the possibility of systemic manipulation--sometimes observable and sometimes not. In all three cases, one encounters not just corruption in typical variation, but the corrosive effects of fakery. That fakery is at its most direct in the instances of self-reflexive corruption; but it is present as well in internal and external corruption--not just in the obvious way--bad data--but in a more subtle way, the effect of bad data on the sense of trust in the system or its integrity. Where the objects of data driven governance lose trust in the truthfulness of the system and in its integrity, it power to effectively manage behavior becomes seriously weakened. One sees that, for example, in current efforts to update the U.S. Census data warehouse (Census Relying on Social Media, Advocates to Stop Bad Info, some of which appears below). In the longer run it is this effect on data confidence, rather than the correctable glitches in data, that provide the greatest threat to automated law. There is a strong parallel here to the challenges of market integrity that is worth exploring.
Examples of each, three drawn from quite recent news stories, follows.
Self-Reflexive Corruption:
Census Relying on Social Media, Advocates to Stop Bad Info
By The Associated Press
Jan. 30, 2020
The U.S. Census Bureau is relying on outside help from social media companies, advocacy groups and other government agencies to halt campaigns that try to discourage people from participating in the once-a-decade head count through the spread of false information, officials said Thursday.
Because the decennial census takes place only once in every 10 years, some people may not be familiar with it. That can lend itself to misinformation and disinformation, said Stephen Buckner, an assistant director of communications at the bureau during a Facebook Live session. Misinformation is the unintentional spread of incorrect information. Disinformation is the deliberate spread of false information.
“It's really, really important that we do it right," Buckner said. “They're are no do-overs, so when the numbers are out, there's a 10 year process until the next count."
The Census Bureau has formed a new “Trust & Safety" team of more than 20 agency staffers who will monitor social media and other platforms for false information about the 2020 census, and then respond swiftly to inaccuracies when needed.
In the past several months, several social media platforms — including Facebook and YouTube — have promised to clamp down on misleading information about the census. On Wednesday, Pinterest joined the effort in announcing it would remove misleading content about who can participate in the 2020 Census and about the 2020 elections.
“If we find a Pin or board that violates our policy, we’ll share it with the Census Bureau so that all the other platforms they’re working with can also take action on the content," Pinterest public policy manager Aerica Shimizu Banks said in a statement. “Similarly, if the Bureau provides verified misinformation or disinformation to us, we’ll look for it on our platform and take anything we find down."
The bureau also is relying on groups like the Better Business Bureau and AARP, and their consumer-protection hotlines, to gather reports on the spread of misleading information, as well as advocacy groups for minorities who may be at risk of being under-counted, said Zachary Schwartz, who is running operations for the bureau's “Trust & Safety" team.
“They're going to expand the bureau's reach into these communities to make sure that when there is a rumor flying around ... they can go right in there and put in authoritative content," Schwartz said.
Members of the public also are being asked to email the bureau at rumors@census.gov if they encounter inaccurate information.
The 2020 census will help determine how $1.5 trillion in federal spending is distributed and how many congressional seats each state gets. The count started earlier this month in rural Alaska. The rest of the nation won't begin participating until mid-March. This is the first decennial census in which the Census Bureau is encouraging most people to fill out the questionnaire online, though people can still answer by telephone or by mailing in their forms.
Fake posts about the census began popping up days after the U.S. Supreme Court ruled last June that the Trump administration could not ask about citizenship status on the 2020 census. In another recent case, posts in neighborhood chat groups warned that robbers were scamming their way into people’s homes by asking to check residents’ identification for the census. That was a hoax, but it left Census Bureau officials scrambling to get the posts removed from Facebook.
Civil rights leaders worry that if misinformation discourages immigrants and minorities from participating in the census, it could leave those populations underrepresented in key government
__________
Consumers are ‘dirtying’ databases with false details
Privacy concerns and unwanted marketing are the top reasons for consumers giving false information online and with only a small percentage of incorrect responses disproportionately devaluing databases, brands need to up the ante in explaining the benefits of giving accurate data.
By Mindi Chahal 8 Jul 2015
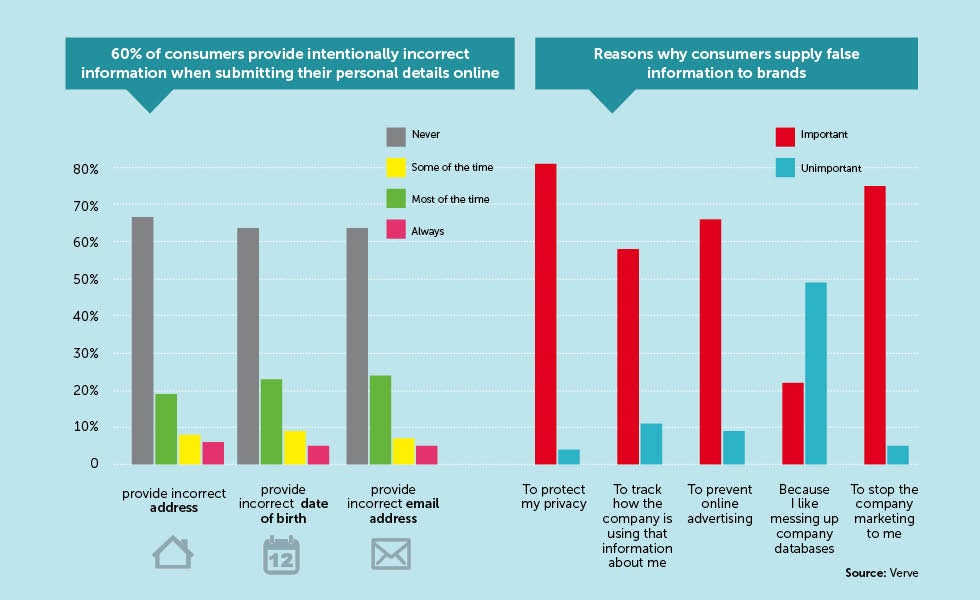
People are deliberately giving brands false data about themselves to protect their privacy, and are ignoring brands’ efforts to empower them to take control of their data, according to a study of more than 2,400 UK consumers by research company Verve.
It only takes a relatively small percentage of database entries to be ‘dirty’ before its value disproportionately declines, according to the report. Companies therefore need to up their efforts to encourage people to give the right information.
The research shows that 60% of consumers intentionally provide incorrect information when submitting their personal details online. Broken down by the types of data provided, birth dates are the most commonly falsified, as almost a quarter of consumers (23%) give the wrong date of birth to companies ‘some of the time’, 9% do this ‘most of the time’ and 5% ‘always’ give the wrong date.
The research also shows that nearly one-third of people give a fake email address and a made-up name at least some of the time. It is a similar story for incorrect information given about home addresses, phone numbers, job titles and company names.
“The upside of providing information has not been articulated,” says managing director at Verve Colin Strong. “The case is not always made by companies about what consumers
are going to get in return for providing information, but people see the immediate effects of being put on more marketing lists and being pursued by online advertising and email spam.”
The study therefore looks at why people give false data. Privacy concerns top the list with 81% of people saying this is important, while 77% believe that the information being requested is intrusive and 76% say it is unnecessary.
Also high on the list of reasons for lying on forms is to stop companies marketing to them – 75% of consumers say this – and two thirds say their motivation for giving false information
is to prevent online advertising. Malice towards companies and embarrassment about having internet browsing behaviour tracked are less common reasons.
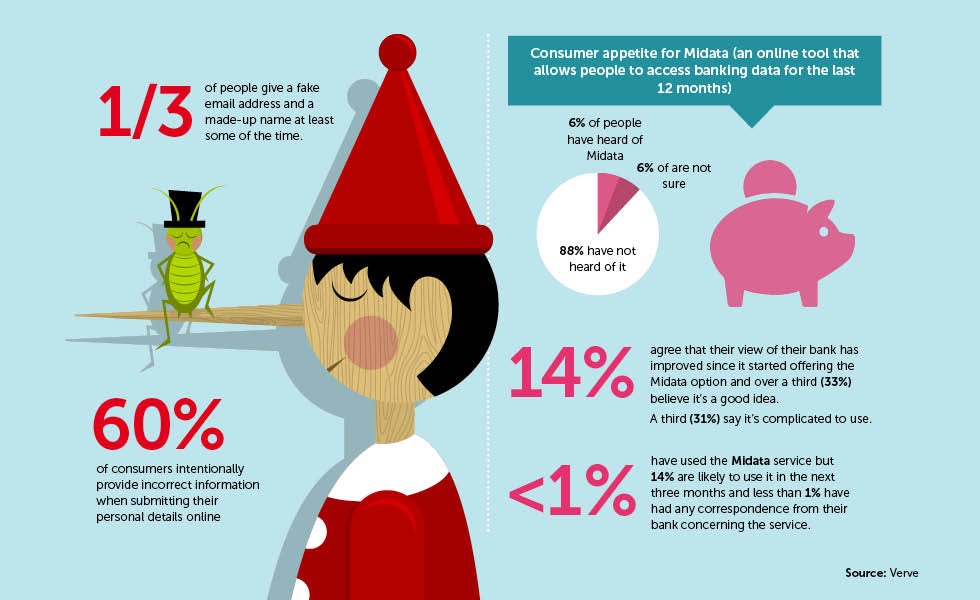
Meanwhile, another study, also by Verve, looks at consumers appetite for Midata, the government-backed scheme tasked with giving consumers access to their personal data which is held by companies such as banks and energy providers. For example, current accounts now make transactional data for the previous 12 months available to download as a single file from online banking websites.
Although it is a form of consumer empowerment, the awareness is low. Only 6% of people have heard of Midata, 6% are not sure and 88% state they have not heard of it. In addition, the stats show that less than 1% say they have used their bank’s Midata service, while 14% are likely to use it in the next three months and less than 1% say they have had any correspondence from their bank about it.
However, there are positive signs for engagement as 14% agree that their view of their bank has improved since it started offering the Midata option and over a third (33%) believe it is a good idea.
Strong says: “With Midata there is a greater opportunity for consumers to recognise what kind of data is available and how it can be used to good effect.”
Consumers also show some interest in what they can use the data for, as 15% agree that they intend to upload the Midata information to a price comparison site in order to get the best banking deal and 14% agree that they intend to upload the information to apps that help them with their finances.
However, many consumers question using the information to get better deals, with 39% agreeing that there is little value in using Midata information to compare bank accounts. Almost a third (31%) say it is complicated to use and 68% agree that they are uncomfortable sharing banking data with third parties such as comparison sites.
“There is a danger of missed opportunity around all of this,” adds Strong. “Banks and mutuals [such as building societies] could help vulnerable consumers, who could do with more guidance and tools to assist the way they manage their finances. It is in their interest to develop propositions in collaboration with consumers.”
__________
Internal Corruption:
California attorney general reviewing LAPD use of state database after reports of false gang IDs:
Threatened with revocation of access, department has agreed to reforms
L to R; Xavier Becerra, State Attorney General, Christine Sun, special assistant to the Attorney General, Jenny Reich, Director of the Bureau of Justice and Ed Medrano, Chief of the Law Enforcement Division at a press conference Monday, February 10, 2020. The Attorney General announced an investigation into the LAPD’s CalGang records after irregularities emerged about those who have been included on the list. (Photo by David Crane, Los Angeles Daily News/SCNG)
By Josh Cain | Southern California News Group
PUBLISHED: February 11, 2020 at 5:38 am | UPDATED: February 11, 2020 at 5:42 am
California’s attorney general said his office will review how the Los Angeles Police Department has been using the state’s CalGang database after some officers last year were found to have been falsifying information about innocent people and labeling them as gang members.
Attorney General Xavier Becerra said Monday if serious abuses are found in the state audit, or if LAPD fails to follow new rules he’s imposing on the agency, that could mean revoking its access to the decades-old system.
“LAPD’s inputs are under a microscope,” he said during a press conference in downtown L.A.
The review comes after LAPD’s chief said internal affairs was investigating at least 20 officers in the Metropolitan Division, an elite crime-suppression unit, who may have been making up information on field interview cards they used to document their observations during stops of drivers or pedestrians.
In some instances, the reviewers found inconsistencies between what happened in those stops and what the officers put down in their reports, said Chief Michel Moore in January while presenting numbers from the city’s 2019 crime report.
At the time, officials said 10 officers under review were stripped of their police powers and sent home. Another 10 were removed from the field and placed on inactive duty.
Just one officer so far has faced internal discipline as a result of the investigation. That officer was due to come before an internal review board, and could get fired.
Moore previously said investigators were looking at hundreds, possibly thousands, of field interview cards submitted by those officers. They were also reviewing thousands of hours of video from the officers’ body worn cameras.
Through that process Moore said he hopes to identify how many times the officers may have lied, and why. So far, he said, most of the stops the officers conducted and the reports they wrote were accurate.
“There’s many instances where the information we’ve looked at is accurate and complete,” he said. “Nonetheless, this is a cleaning… We’re going through the entire list.”
LAPD’s investigation was launched early in 2019 after a mother in Van Nuys complained to commanders at a local police station that her son was added to the CalGang database.
She insisted he was not a gang member. After a commander reviewed an officer’s field interview card and footage from the stop, he found the man was wrongly added to the system.
When he alerted LAPD leadership to the issue, an investigation found other officers who associated with the first officer may also have been purposely inputting misleading information about people into CalGang.
LAPD and dozens of other law enforcement agencies have been using the database for around two decades, officials with the Attorney General’s Office said.
CalGang allows local police to enter the names of people who are gang members themselves or who they believe have connections to gangs.
In practice, that has meant even family members and friends of gang members have had their names added to the database. A 2016 state audit found children as young as 1-year-old being put into the system.
The audit prompted legislators to give the Attorney General’s Office more control over how to operate CalGang. At the time, around 150,000 people were in the system — a purge initiated by Becerra reduced that number. There are now around 80,000, officials said Monday.
Becerra said Monday the new rules allow him to increase oversight over LAPD and other police agencies, though he would not say if any other police departments around the state are being audited as well.
Police officials statewide have said there are enough controls on how they’re allowed to use the system to limit abuse.
Edward Medrano, the former chief of police for Gardena who now works for the Attorney General’s Office and will assist in the state audit of LAPD, said CalGang cannot be used by police to prove anyone is a gang member — the system is an investigative tool, and not meant to be punitive.
“You still have to use evidence in a court to prove someone is a gang member,” he said.
Becerra outlined an agreement reached with LAPD to monitor its internal review and changes to its oversight of how officers are using CalGang.
In a letter to Chief Moore, Becerra said LAPD agreed to conduct a detailed inspection of its records, develop new oversight procedures, retrain its officers and require additional reviews by local commanders. At the end of the review, Becerra said he could revoke or suspend LAPD’s access to CalGang, or in a more limited step send a letter censuring the police department.
In a statement Monday, LAPD officials said they were cooperating with the DOJ review.
LAPD is one of the biggest law enforcement agencies in the country and is the largest user of the CalGang system statewide, Becerra said. He said removing them from the database would be “a big hit” to its viability.
“Clearly there were problems with the database,” Becerra said. “We are trying to make sure we get this right.”
__________
External Corruption
Justice Department announces 4 Chinese military officers indicted in Equifax hack: Officials say some 150 million Americans were affected.
ByLuke Barr
February 10, 2020, 12:27 PM
4 min read

Equifax data breach may have been state-sponsored crimeCatch up on the developing stories making headlines.Sarah Silbiger/Getty Images
The Justice Department on Monday announced that four Chinese military officers have been indicted with hacking the credit company Equifax in 2017.
The breach compromised the personal information of some 150 million Americans, one of the largest data breaches in history, officials said.
“It came to light in the summer of 2017, when Equifax announced the theft. The scale of the theft was staggering. As alleged in the indictment, the hackers obtained the names, birth dates, and Social Security numbers of nearly 150 million Americans, and the driver’s license numbers of at least 10 million Americans. This theft not only caused significant financial damage to Equifax, but invaded the privacy of many millions of Americans, and imposed substantial costs and burdens on them as they have had to take measures to protect against identity theft,” Attorney General William Barr said at a news conference announcing the charges.

Attorney General William Barr participates in a press conference at the Department of Justice along with DOJ officials, Feb. 10, 2020 in Washington, DC.Attorney General William Barr participates in a press conference at the Department of Justice along with DOJ officials, Feb. 10, 2020 in Washington, DC.Sarah Silbiger/Getty Images
According to an indictment unsealed in the Northern District of Georgia, the hackers, members of China's People's Liberation Army, exploited a vulnerability in the Equifax network, which led to the hack.
Deputy Director or the FBI David Bowdich said that none of the information stolen has been used maliciously.
The four men are also charged with stealing trade secrets of a database the company developed.

Wu Zhiyong, Wang Qian, Xu Ke, and Liu Lei face charges of computer fraud, economic espionage, and wire fraud for their role in one of the largest thefts of personally identifiable...
Wu Zhiyong, Wang Qian, Xu Ke, and Liu Lei face charges of computer fraud, economic espionage, and wire fraud for their role in one of the largest thefts of personally identifiable information by state-sponsored hackers ever recorded.Federal Bureau of Investigation
The indictment alleges that the hackers exploited a known vulnerability in the Apache Struts software used by Equifax and that vulnerability was not patched prior to the data breach.
According to the indictment, “On or about March 7, 2017, Apache announced a vulnerability in certain versions of Apache Struts software that permitted unauthorized users to access the Apache Struts Web Framework and perform a remote code execution attack on a target web application.
"The United States Computer Emergency Readiness Team issued a threat warning notice about the vulnerability on or about the following day. The vulnerability was not patched on Equifax’s online dispute portal.”
“We are grateful to the Justice Department and the FBI for their tireless efforts in determining that the military arm of China was responsible for the cyberattack on Equifax in 2017," Mark Begor, Chief Executive Officer of Equifax, said in a statement. "It is reassuring that our federal law enforcement agencies treat cybercrime – especially state-sponsored crime – with the seriousness it deserves, and that the Justice Department is committed to pursuing those who target U.S. consumers, businesses and our government. The attack on Equifax was an attack on U.S. consumers as well as the United States," he said.
ABC News' Alexander Mallin and Jack Date contributed to this report.



No comments:
Post a Comment